How can you increase password security?
Passwords are the keys to our digital identities. A strong password serves as the first line of defense against cybercriminals. However, statistics show that 36% of UK respondents reuse passwords across 5 to 10 sites and that 35% admitted to resetting their passwords every day or multiple times a week.
- Regular virus scans
- Automatic backups and simple file recovery
What are the requirements for password security?
Many people still rely on weak or easily guessable combinations for their passwords. To ensure a high level of password security, several factors should be considered. Choosing a secure password and using a password manager can be regarded as fundamental aspects of password security.
What makes passwords secure?
Although secure passwords alone cannot provide absolute protection against attacks by cybercriminals, creating a secure password is still crucial for safeguarding your accounts. Users can check whether their chosen password is secure by following a range of criteria:
- Length: The length of a password plays a critical role, as longer passwords are exponentially harder to crack than shorter ones. A strong password should be at least 12 to 16 characters long.
- Complexity: A secure password should include uppercase and lowercase letters, numbers, and special characters such as @, #, or $. This variety makes it more difficult for both humans and automated tools to guess the password.
- Unpredictability: Avoid simple patterns or recognisable words in passwords, as cybercriminals often use dictionary attacks, testing common passwords.
- Uniqueness: Do not reuse passwords across multiple services and platforms. Instead, use unique passwords for each web service.
- Regular updates: Especially for critical services, updating passwords regularly can reduce the risk of exploitation due to previous security breaches.
Choosing the right password manager
Password managers are practical tools for generating and securely storing complex passwords. When selecting the right password manager, ensure it supports end-to-end encryption and includes features such as breach alerts or security audits. Regular updates are another indicator of a trustworthy password manager.
Major password leaks in recent years
Every day, we entrust vast amounts of sensitive data to companies and technology, with passwords often being the sole protection—one that, it seems, is not taken seriously enough. This is evident from the numerous data breaches in recent web history. Cybercriminals have repeatedly accessed login credentials using methods like malware, phishing emails, or brute-force attacks, stealing confidential user data. Below is an overview of some of the most significant incidents:
- LinkedIn (2012, 2016): LinkedIn was hacked in 2012, resulting in the theft of over 6.5 million hashed passwords. In 2016, an additional 117 million login credentials from this hack surfaced on the dark web.
- Yahoo (2013, 2014): One of the largest security breaches ever affected Yahoo. Between 2013 and 2014, a total of three billion accounts were compromised, including usernames, passwords, and security questions.
- Adobe (2013): More than 150 million Adobe user accounts were stolen during a breach, with many of the passwords poorly encrypted.
- Facebook (2019): Facebook revealed that millions of user passwords were stored in plain text on internal servers. Although the data did not leak externally, the incident highlighted the need for secure practices even at the company level.
- Collection #1-#5 (2019): In January 2019, over two billion email addresses and passwords from various sources, including known and previously unknown leaks, were published as part of this mega-leak.
- Twitter/X (2022): A security breach exposed personal data from over 5.4 million accounts, including phone numbers and email addresses, due to a bug.
- RockYou (2024): RockYou2024 was a massive leak, considered one of the largest ever published, comprising over 9.9 billion passwords compiled from various sources.
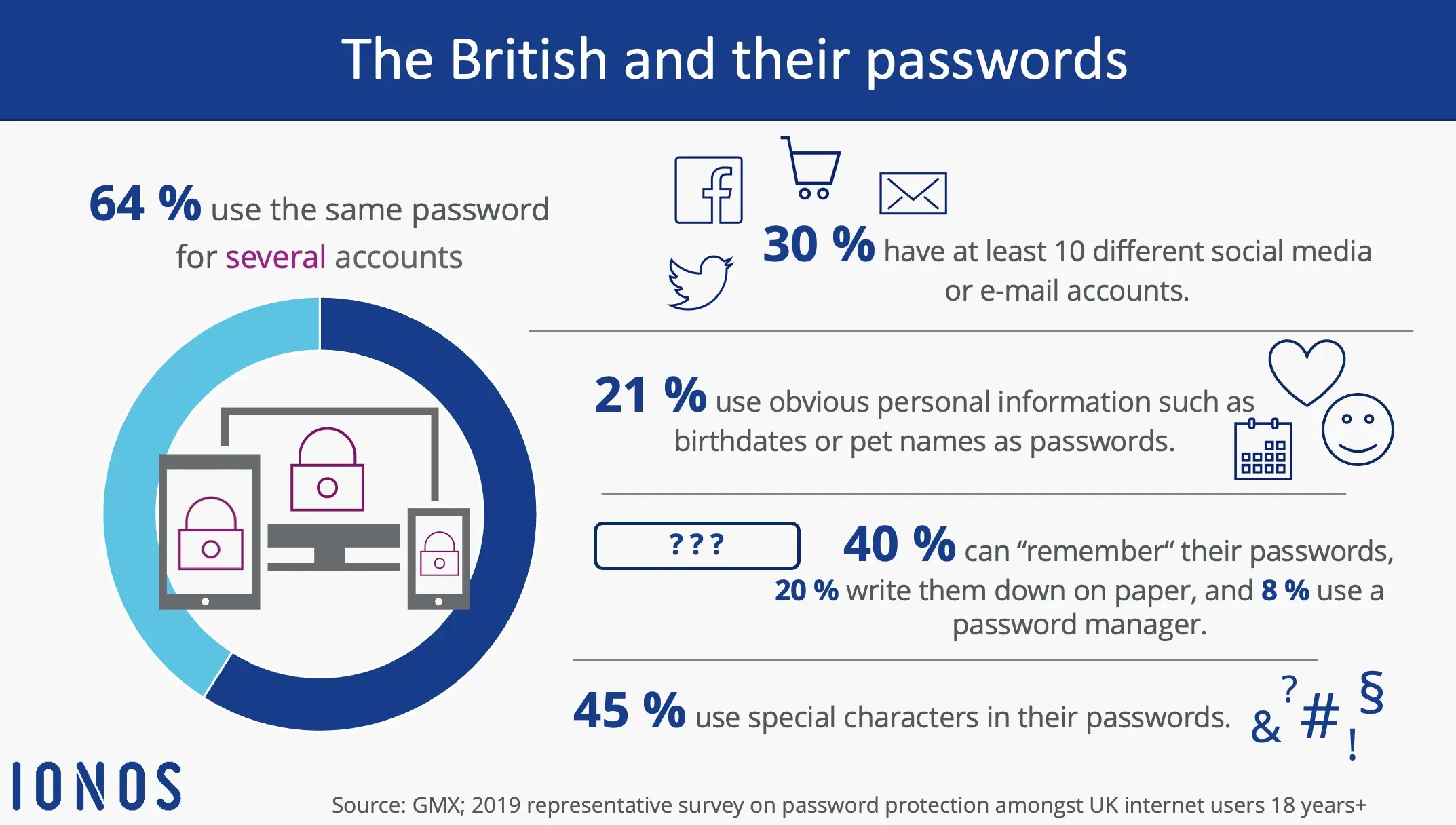
These events underscore the critical importance of cybersecurity. The results of a representative survey conducted by GMX of 1,050 people are all the more astonishing: 64% of people stated that they use the same password for some, or even all, of their online accounts, while only 21% use a different password for each of them. The 2019 GMX study also revealed that 9% had never even changed their main email account password, which leaves them very vulnerable.
For their attacks, cybercriminals often do not use their own computers but instead exploit the devices of unsuspecting users. These devices are infected with malicious software, allowing attackers to remotely control them. Such compromised systems, often referred to as bots or zombies, are organised into large networks.
How to check password security
Checking the security of your passwords is a crucial step in protecting your digital accounts from unauthorised access or after data leaks. There are various methods and tools available to check whether your passwords have been compromised, meet current security standards, or are too weak.
Online services for data leak checks
- Have I Been Pwned (HIBP): One of the most well-known and trusted platforms is Have I Been Pwned (HIBP). Here, you can check whether your email address or password has been compromised in a known data breach. By entering your email, you will receive a list of websites affected by leaks where your data may have been stolen. The site also allows direct password checks, ensuring anonymity through specialised hashing technologies.
- Google Security Check: Google offers an integrated password-checking feature in Chrome. The browser alerts you if any of your saved passwords have been part of a data breach. Additionally, you can perform a comprehensive security check via your Google account, which also identifies weak or reused passwords.
- Security features of password managers: Many modern password managers offer a function to check your stored passwords. These tools scan for weaknesses, duplicated use, and known security incidents. This way, you get a clear overview of which passwords need updating.
Testing password strength
Besides checking for data leaks, it is essential to evaluate the strength of your passwords. Numerous tools can assist with this by assessing the length, complexity, and entropy (randomness) of a password. These services also simulate how long it would take to crack your password using a brute-force attack. For example, the password 123456 can be cracked in less than a second whereas a stronger password like X$4g8JwQ!a_%j could withstand attacks for many years.
Manual review and monitoring
If you know that a particular platform has been affected by a data breach, check whether you have an account on that platform. Change your passwords immediately, especially if you have reused them on other websites. It is also helpful to follow cybersecurity news or platforms like Reddit (e.g., the subreddit [r/netsec]) to stay informed about new data breaches. Security vulnerabilities are often reported there earlier than through official channels, allowing you to take preventive measures in time. Additionally, tools like HIBP offer email notifications that alert you when your email address appears in a new leak.


