DNS over HTTPS
The Domain Name System (DNS) is a proven solution. Users only need to enter a recognisable web address into their browser, and the system finds the corresponding IP address within a short period of time. To do this, various name servers are accessed which store the numerical address that corresponds to the URL. Although it is still fully functional in principle, the DNS is somewhat dated. Developed several decades ago, today’s security concerns had not yet arisen.
From today’s perspective, however, the DNS is not secure. Requests are generally transmitted unencrypted and can be read by anyone. This means that a cybercriminal could use his own server to intercept a victim’s DNS relatively easily. Called DNS hijacking, these attacks transfer users to websites that either release malware, phish for data, or annoy users with large amounts of advertising. That’s why DNS over HTTPS (DoH) is being discussed among industry experts as a viable alternative. But could the protocol make the Internet more secure?
Why do you need DNS over HTTPS?
DoH makes it possible to achieve several objectives including increased security. By running the DNS using the secure HTTPS protocol, the primary objective is to strengthen the user’s security and privacy. By using the encrypted HTTPS connection, it should no longer be possible for third parties to influence or spy on the decryption. A fraudster would thus be unable to view requested URLs or change them.
On the one hand, this strengthens the fight against cybercrime and, on the other, makes it harder to censor the Internet. Some governments use DNS to block certain websites to restrict freedom of expression or impose local Internet regulations – for example, anti-pornography laws.
Some Internet providers (ISP) use DNS hijacking technology on purpose to serve error messages if a user enters a web address that cannot be decrypted (because of a typo, for instance). Some ISPs intercept this and instead direct the user to their own website that advertises their own or third-party products. This is neither illegal nor does it directly damage the user or their devices, but the redirection could be perceived as disruptive.
But changes to DNS would also improve its performance. The DNS protocol is no longer considered to be very reliable. The Transmission Control Protocol (TCP) in DoH reacts faster when data gets lost during transmission.
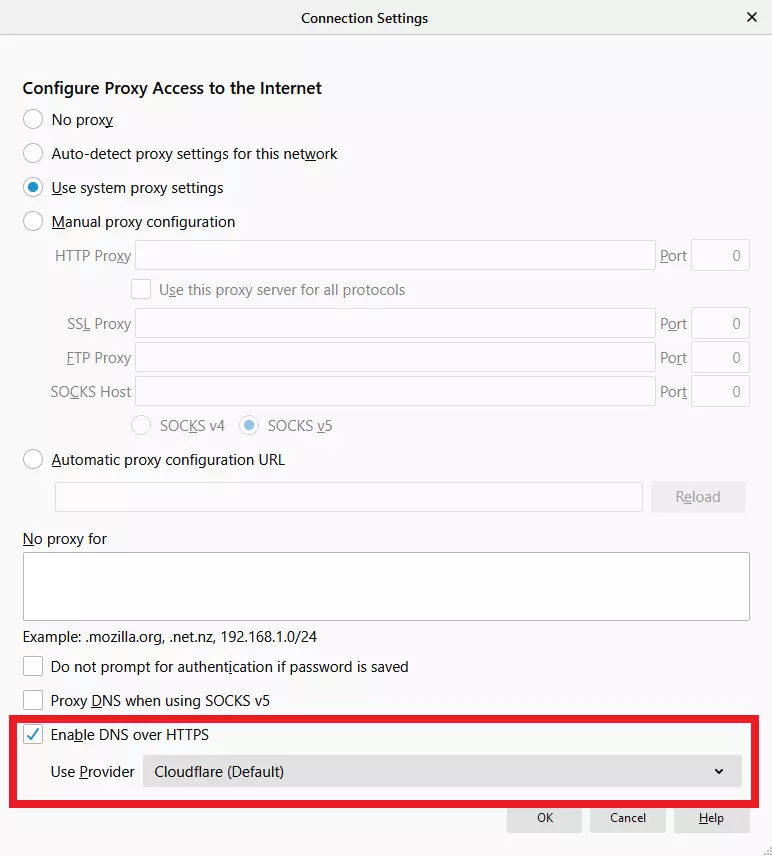
DNS over HTTPS is not yet a global standard on the Internet. Most connections still rely on DNS. So far, Google and Mozilla are two companies that have ventured into the field. As of Firefox version 62, for example, DoH can be activated optionally. Google is currently testing the system with select users. In addition, there are apps for mobile devices that enable surfing via DoH. Android Pie provides an option to enable DNS over HTTPS via the network settings.
How does DNS over HTTPS work?
Some name decryptions can be carried out directly from a user’s device. The corresponding information is shown in the cache of the browser or the router. Everything that has to be transmitted online usually passes through a UDP connection. This allows for a fast exchange of information. However, UDP is neither secure nor reliable. Data packets are regularly lost when using the protocol because there are no mechanisms that guarantee the transmission.
DoH, on the other hand, relies on HTTPS and, therefore, also on TCP – a protocol that is used much more frequently on the Internet. The advantages include encryption of connections and the protocol ensures a guaranteed transfer of data.
With DNS over HTTPS, communication always takes place via Port 443, which is where the actual web traffic is transmitted (e.g. accessing websites). Therefore, an outsider cannot differentiate between DNS requests and other communications. This introduces an additional level of user privacy.
DNS over HTTPS was defined in RFC 8484.
Advantages and disadvantages of DNS over HTTPS
The advantages of the new system are obvious. The technology improves security and user privacy. Compared to classic DNS, DoH provides encryption. However, DNS over HTTPS is neither completely safe nor completely private. As before, all information can still be viewed on the name servers where the name decryption takes place and a number of servers also learn who is requesting what information. Therefore, DNS participants must be trusted with the new technology.
However, DNS over HTTPS shifts responsibilities here. Internet providers’ servers typically oversee a large part of the name decryption. With DoH, on the other hand, browser developers can now decide which servers they want to forward their DNS queries to. In Chrome, this is done using Google’s own DNS server. Mozilla already uses Cloudflare for Firefox. Whilst this raises the question of whether users should trust these companies more than the ISP, it also means that just a handful of providers are in charge.
DoH critics believe that net neutrality is at risk with the DoH. They fear that Google could, for example, answer queries about the company’s own services faster than DNS queries about other websites. By concentrating on a handful of providers, DoH servers also pose a security risk because this would make it much easier for attackers to paralyse the entire DNS.
DoH vs. DoT
In addition to DNS over HTTPS, another technology for securing the domain name system is currently being discussed: DNS over TLS (DoT). The two protocols appear similar at first because both promise greater user security and privacy. But the technologies differ in a few points, including the commitment they’ve attracted from different interest groups. While DNS over HTTPS is primarily based on Mozilla, Google, and providers of private DoH servers, DoT is promoted by the Internet Engineering Task Force (IETF).
On a technical level, DoT differs from its competitors in that it establishes a TLS tunnel instead of an HTTPS connection. It also uses a different port. As mentioned above, while DoH runs via Port 443, communication with the DNS via TLS takes place via the separate Port 853.