What is Ethernet (IEEE 802.3)?
Ethernet describes a technology for cabled data networks that connect software and/or hardware with each other. This mostly takes place via LAN cables, which is why Ethernet is also sometimes referred to as LAN technology. In this way, Ethernet enables data exchanges between end devices. These could be computers, printers, servers, routers, or others. When combined into a local network, these devices establish connections via the Ethernet protocol and can exchange data packages with one another. The current and most widely distributed protocol is IEEE 802.3.
Ethernet was developed back in the early 1970s, but the network system was originally only used internally by the company Xerox. At the start of the 1980s, Ethernet was developed into a standardised product. However, Ethernet still wasn’t widely used until the middle of the decade when several manufacturing companies started to work with Ethernet and related products. The technology made a significant contribution to the way that the personal computer revolutionised the working world. Today, the widely-distributed IEEE standard 802.3 is used in offices, private households, containers, and carriers.
While the first version of the technology only had a speed of 3 megabits per second, Ethernet protocol today enables speeds of up to 1.000 megabits per second. Earlier Ethernets were limited to a building, but today Ethernet can cover a range of just over 6 miles with the use of fiber optic cables. Over the course of its development, Ethernet has taken over a dominant role among LAN technology and outperformed various competitors. In addition, today real-time Ethernet is the industry standard for communication applications.
Ethernet refers to a technology that allows devices connected by cables within a data network to communicate with one another. In an Ethernet, connected devices can build a network and exchange data packages. In this way, a local network (LAN) is created via Ethernet connections.
How does Ethernet work? Then and now
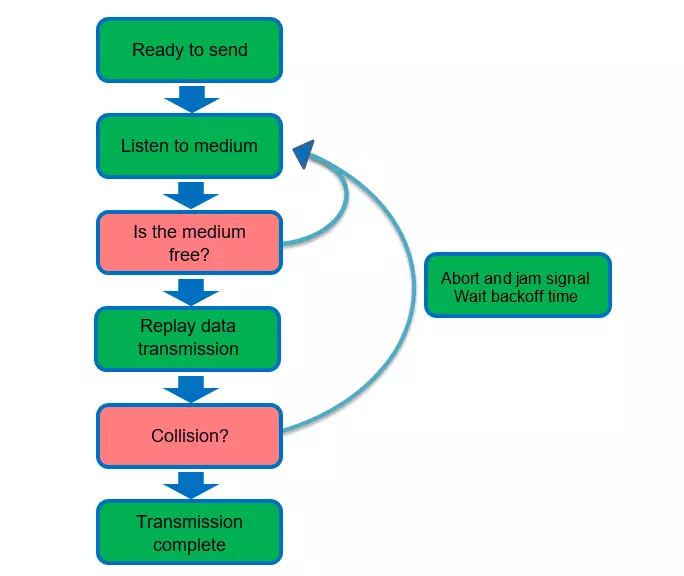
Every device in an Ethernet network receives its own 48-bit address, called the MAC address. Participants in the same network can exchange high-frequency messages. For this, Ethernet uses baseband and multiplexing. The smooth CSMA/CD (carrier sense multiple access/collision detection) algorithm is used for communication with one another. The network topology of Ethernet is logical, so the structure can be implemented as a bus or star, for example.
Communication with this algorithm is similar to a round table discussion, where each participant lets the other speak out. If two messages collide, then the participants try to send them out again at random intervals. Because a communication has to be sent as well as received to be successful, there can’t be any data jams – for example, if a sent message is too strong for a relatively weak reception performance. Otherwise, data may be lost. Signal speed and transfer rates control the smooth communication by defining rules for the data frames.
To prevent a data collision, a corresponding signal has to reach the receiver before the data package. Because most networks these days function in full-duplex mode, though, this is rarely a problem. But it was quite important for the earlier development of the Ethernet technology.
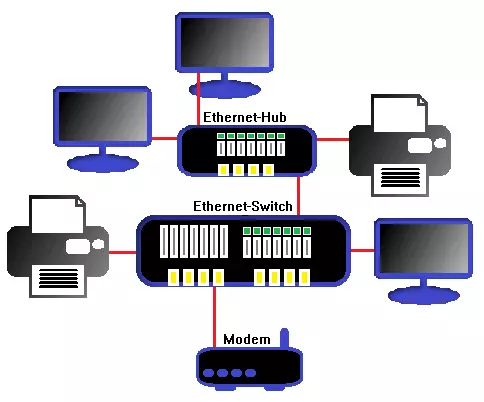
Originally, each message that was sent within a network went to all connected devices. These then had to filter through all received data and decide whether it was relevant to them. This common bus enabled broadcast messages, but also recorded all data traffic for each member – clearly a security gap of early Ethernet. Data could be encrypted, but data traffic itself couldn’t be individually controlled. Hubs also couldn’t close this security gap. Bridges and switches are a solution in modern networks, as they can be used to segment the Ethernet.
This technology doesn’t solve all problems, though. Abuse by MAC flooding or MAC spoofing, for example, still poses a danger for the stability of the network and the security of the communicated data packages. Working securely with Ethernet therefore requires serious use of all connected systems and regular data analysis (e.g. LAN analysis) to uncover potential cases of misuse or disturbances.
As long as an Ethernet’s data amount isn’t at capacity, it functions well. Capacity utilisation rates of more than 50 percent can cause data jams, though. As personal computers developed technologically and continuously increased their data volume, Ethernet networks also had to develop further to keep pace with the progress of technology. Switches are responsible for efficiently dividing data packages and minimising the risk of collisions. Modern cable technologies like twisted pair and fiber optic have higher transfer rates meet the modern requirements for a network.
Another innovation is ‘Ethernet flow control’. With this mechanism, data transfer can temporarily be stopped to alleviate data flow from another location. This is especially practical in full-duplex mode when a network serves a relatively high number of end devices. The flow control for specific members of the network is temporarily cut off to optimise the overall reliability of the network. This can also cause losses in speed, though, which can then be stemmed by other mechanisms such as the transmission control protocol.
In the past, Ethernet primarily used conventional coaxial cables. Today, twisted pair copper cables and fiber optical cables are the industry standard, as they enable much faster transfer rates and a larger range. Another advantage is that copper cables can also supply power to connected devices. This method, called ‘power over Ethernet’ (PoE), is specified in IEEE 802.3af and enables energy-efficient networks.
The history of Ethernet
Ethernet developed from ALOHAnet, a radio-based network from the University of Hawaii. In the Xerox Palo Alto Research Center, the visionary Robert Metcalfe was already working on an early version of the cabled Ethernet protocol at the beginning of the 1970s. It was intended to make work within the company easier first, and then be actively tested. The test phase peaked in 1976 with a scientific paper, published by Metcalfe together with David Boggs. It described local networks of connected personal computers.
In 1979, Metcalfe founded his own company 3com to push forward with the development of computers and LAN and establish Ethernet as standard. In 1980, he made his breakthrough with the adoption of Ethernet 1.0, which was then further developed by the Institute of Electrical and Electronics Engineers (IEEE). This process led to the invention of other technologies, including the CSMA/CD (carrier sense multiple access/collision detection) protocol, which later became known as IEEE 802.3. It also brought about the groundbreaking protocols token bus (802.4) and token ring (802.5).
Between 1983 and 1986, the innovations Cheapernet, Ethernet-on-Broadband, and StarLAN arrived on the scene before the Ethernet standard had started to receive more attention from many manufacturers. As a result, some small companies started to use Ethernet networks in the workplace, but still via telephone-based four-wire lines. Ethernet connections via twisted pair and fiber optic cables weren’t developed until the early 1990s, which lead to the introduction of the 100 MB/s standard for Ethernet according to IEEE 802.3u in 1995. A standard for wireless LAN (802.11) was adopted at the same time. 1995 is considered the birth year of the modern internet.
Overview: Ethernet technologies and terms
| Technology/Term | Explanation |
|---|---|
| LAN (local area network) | Computer network that locally connects multiple systems with one another |
| Switching | Switching regulates the path of a data package in the network; Entrances and exits for packages are defined according to sender and receiver |
| Ethernet flow control | Data transfer in the Ethernet is temporarily stopped; The goal is less data loss and more efficiency |
| CSMA/CD (carrier sense multiple access/collision detection) | Media access method that determines which systems in a network may access a transfer medium; prevents collisions |
| Ethernet frame/data frame | Protocol unit that contains important information for data transmission, including MAC address |
| MAC address/device address | Uniquely assigned address for each device in the computer network |
| PoE (power over Ethernet) | The Ethernet cable can provide the target device with power |
| Coaxial cable | Two-layer cable, up to 10 MB/s (outdated technology) |
| Twisted pair cable | Cable with twisted wire pairs, enables PoE, up to 10 GB/s |
| Fiber optic cable | Optical fiber, high range, enormous transmission rates possible (theoretically up to 70 TB/s) |
| Half-duplex mode | Communication can only be sent in one rotating direction |
| Full-duplex mode | Communication is sent in both direction at the same time |
Overview: Ethernet standards
| Ethernet standard | Designation | Data rate | Cable technology | Release year |
|---|---|---|---|---|
| 802.3 | 10Base5 | 10 MB/s | Coaxial cable | 1983 |
| 802.3a | 10Base2 | 10 MB/s | Coaxial cable | 1988 |
| 802.3i | 10Base-T | 10 MB/s | Twisted pair cable | 1990 |
| 802.3j | 10Base-FL | 10 MB/s | Fiber optic cable | 1992 |
| 802.3u | 100Base-TX100Base-FX100Base-SX | 100 MB/s | Twisted pair cable, fiber optic cable | 1995 |
| 802.3z | 1000Base-SX1000Base-LX | 1 GB/s | Fiber optic cable | 1998 |
| 802.3ab | 1000Base-T | 1 GB/s | Twisted pair cable | 1999 |
| 802.3ae | 10GBase-SR10GBase-SW10GBase-LR10GBase-LW10GBase-ER10GBase-EW10GBase-LX4 | 10 GB/s | Fiber optic cable | 2002 |
| 802.an | 10GBase-T | 10 GB/s | Twisted pair cable | 2006 |